What Do Phishing Emails Look Like?
What do Phishing emails look like? It's an interesting question, and it used to be easily answered. When Phishing emails first began to show up in our mailboxes, they were easily identified (though sadly some people still fell for them).
In the good old days, we'd get lots of notes from the Nigerian prince who needed your bank information to free up his millions of dollars; or the eastern European who desperately wanted to overpay for your car, and your friend sending an SOS, because they had lost their phone, wallet, etc. but was able to email but only email.
The generic and fantastic nature of these emails was such that the spam and malware filters were able to adapt and mainly filter them out before they arrived in your inbox. It was this ability – to spot the obvious — from which the many email security companies declared their abilities to thwart ALL types of attacks, including phishing. However, as we learned in our research for our 2019 Special Phishing Report, that declaration couldn't be further from the truth.
The reality is many of those applications which are advertising as phishing attack prevention are failing miserably in practice. They are failing because the nature of phishing attacks has changed dramatically. Indeed, the generic prince emails and mass spamming events still happen, but phishing attacks today are highly targeted, infinitely intelligent, and wholly unique. The criminals know many of the tricks to avoid falling into the quarantine folder. Moreover, cyber-criminals quickly shift and change their methods all the time once their tactics are spotted. Most of these mass-market anti-phishing solutions use dated Bayesian statistical methods the seek out common patterns. This is great for spam detection but useless against phishing.
2019 Special Phishing Report
Based on our analysis, which is outlined in our 2019 Special Phishing Report …" the three widely-used SEGs (Security Email Gateways) we examined allowed over 16,000 malicious phishing emails through in four months." 16,000! It is staggering that three different, self-declared phishing attack software solutions allowed 16,000 actual phishing emails into inboxes across their customer base. The obvious question is, why? How could phishing attack software solutions allow so many confirmed phishing emails to pass through their filters?
The answer is simple – they don't know what a phishing attack looks like. Modern phishing attacks are not obvious; they are generic stamp outs with questionable spelling and grammar and generic calls to action. Modern Phishing attacks are disguised to fool the spam filters deliberately. Consider the AT&T example from our 2019 Special Phishing Report:
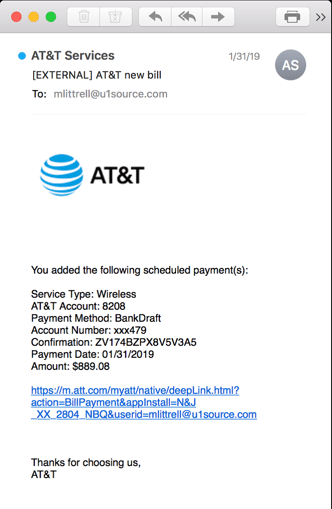
In this case, the call to action is incredibly devious. Rather than ask for the purported victim to update a password or open a suspicious file, the criminal cleverly creates a false narrative and suggests that the victim has just made an $899 payment to AT&T.
The email looks like a receipt. Unless you are calling your relatives in Tasmania for 14 hours a day every day, for two months, the chances you have a phone bill that large are pretty slim. Plus, if AT&T is not your phone company, there is even further reason to be suspicious, and even further reason to click on the link.
Did you follow that? This phishing attack was a fake email, presenting the reader with a fake bill, that they'd almost certainly click. It is conniving right? Pretty convincing too, so compelling that the incumbent phishing attack software solutions failed miserably and allowed it to be delivered.
INKY Is A Better Way
INKY caught it though, in fact, those 16,000 successfully delivered phishing emails were all caught.
Why? INKY knows what a phishing email looks like.
The technology baked into our Phish Fence phishing software solution is peerless, we don't rely on tired algorithms, we don't snoop the phishing aggregator sites for yesterday's news, we stop phish dead in their tracks with our novel technology.
In the case of the AT&T email, our computer vision engine was able to determine that the email was a brand forgery. Further, our machine learning and artificial intelligence engines combined determined that the otherwise legitimate-looking link was, in fact, a rouse designed to take the victim down a path that would ultimately lead to compromised credentials and financial information. INKY follows every link in every email to ensure that it is from the brand it purported to be from.
Knowing what a phishing email looks like is important. Awareness training, and spam and malware filtering can only take you so far, and legacy SEG's are simply not taking you far enough these days to adequately protect employees from falling victim to an attack. INKY can be installed and operational in less than an hour.
You are 60 minutes away from phish free nirvana. Give us a call or request a demo!



