When you hear an anecdotal story of a distant acquaintance being snagged by a Phishing attempt it often conjures a questioning of their smarts, but friends there is little about today’s catch that even the most phishing aware would immediately spot, further as we’ll show below, Phish Fence caught this beauty long before anyone else even noticed.
What happens when someone clicks on a phishing attempt?
In the world of cybercrime 3 hours is a lifetime, in seconds bank accounts can be emptied, billions lost, companies destroyed lives ruined. Can your organization afford three hours? I ask because today’s catch of the day was snagged by INKY a full three hours before its content was picked up by the malware aggregators. This particularly smelly phish is a clever attempt at brand forgery, they’ve got the branding spot on and many of the links are legitimate, clicking on them takes the unsuspecting victim to actual Wells Fargo website pages. Let’s break it down:
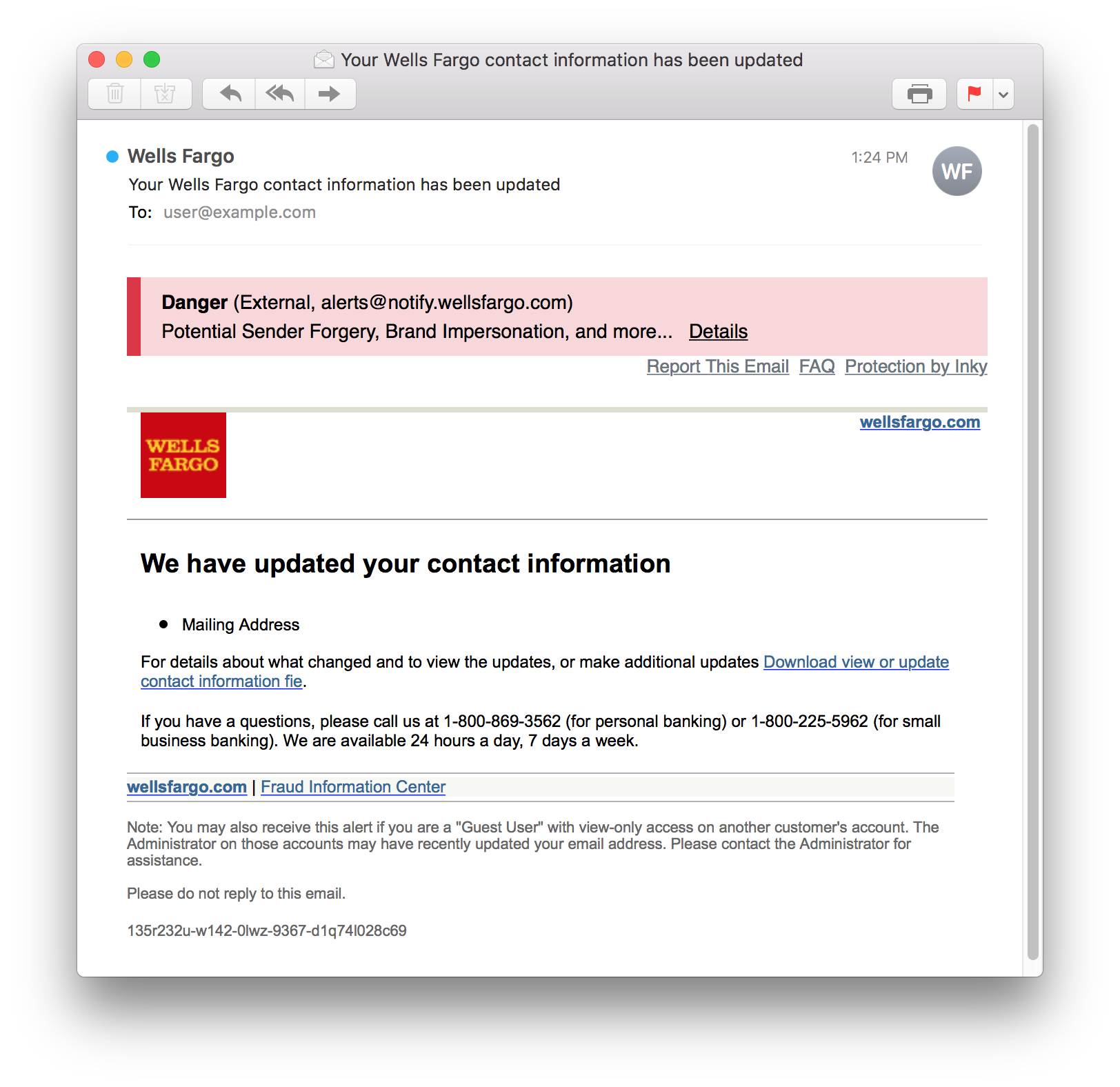
The first thing that struck me was the email address – it looks completely legitimate – would your training program graduates have caught it? Unlikely… but Phish Fence immediately recognized it as a component of the brand forgery.
How to check if a link in an email is safe
The links are all legitimate (except the call to action), the branding and fonts are correct and even the 1-800 number takes you to an actual Well Fargo operator. The call to action, updating your address seems fairly low risk, the curiosity of your address having been updated – without your permission – is a pretty strong motivator to go ahead and click.
Once clicked you get the opportunity to download a file and update your address, easy right? With Phish Fence installed even a user who ignored the giant red banner would be challenged again before initiating the download, those without Phish Fence... not so lucky. Here is an image of where the call to action would take you:
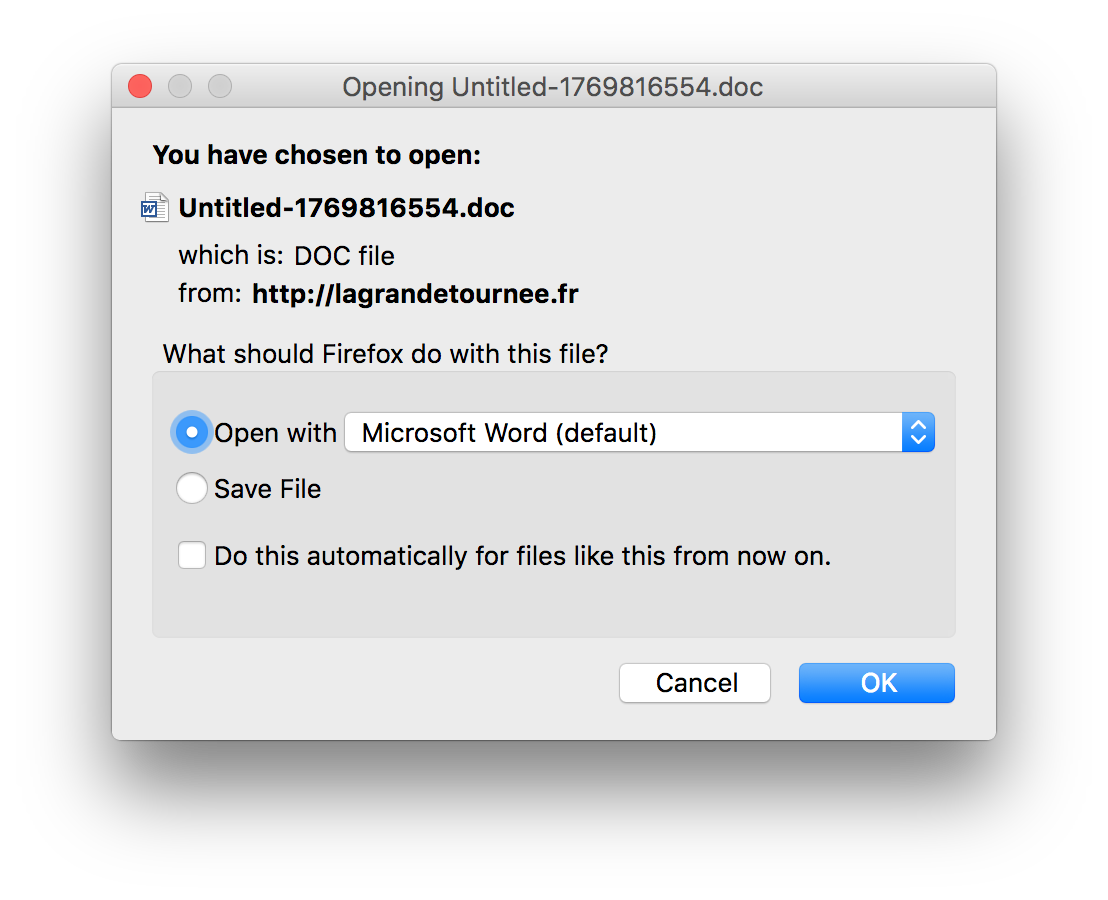
Those unfortunate enough to download the attachment are infected with a pretty nasty malware that allows remote accessing of files and various other nefarious and dangerous intrusions into the victims PC.
The brazen nature of this effort speaks to the evolution of Phishing attacks, they are more mature and more cynical than ever, relying on traditional email protection software and training is no longer good enough, this effort wasn’t even picked up as malware for a full three hours after Inky caught it.
INKY isn’t lucky, INKY is smart, Phish Fence catches things that you or I would miss, it catches phish that swam freely right through traditional defenses for a full three hours. Are you 100% sure that your mailbox is safe? How many hours will go by before your security system alerts you?
Talk to one of our experts today to learn more about how easy it is to have INKY protect your organization's inboxes from phishing attacks.




