I can’t resist writing this blog!! Today’s Catch of the Day falls under one of the many tactics that cyber criminals utilize to bait users into taking action.
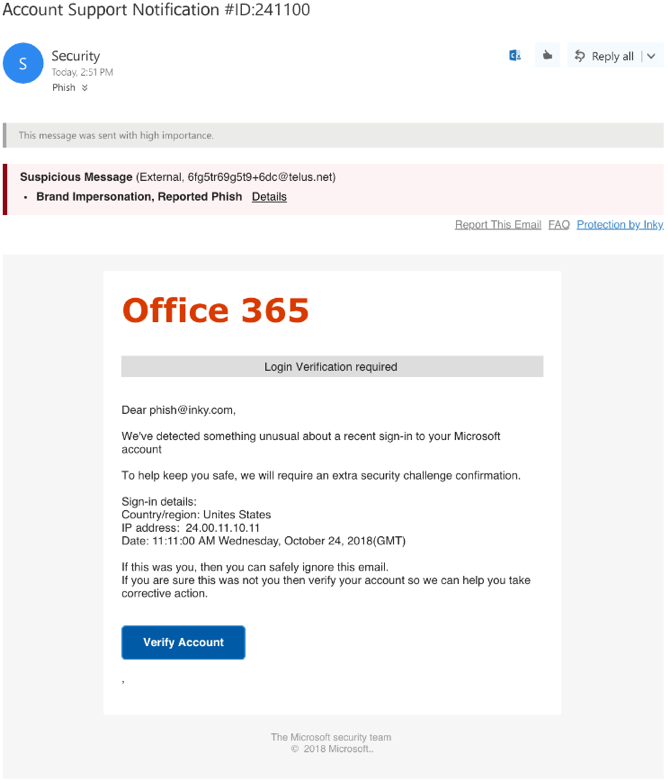
Fortunately for one of our clients, INKY’s Domain Spoofing Detection is so sophisticated, that INKY caught this one, despite them also running a legacy email security solution. The screenshots below show what the mail looks like to the human:
And this is what it looks like under the hood.
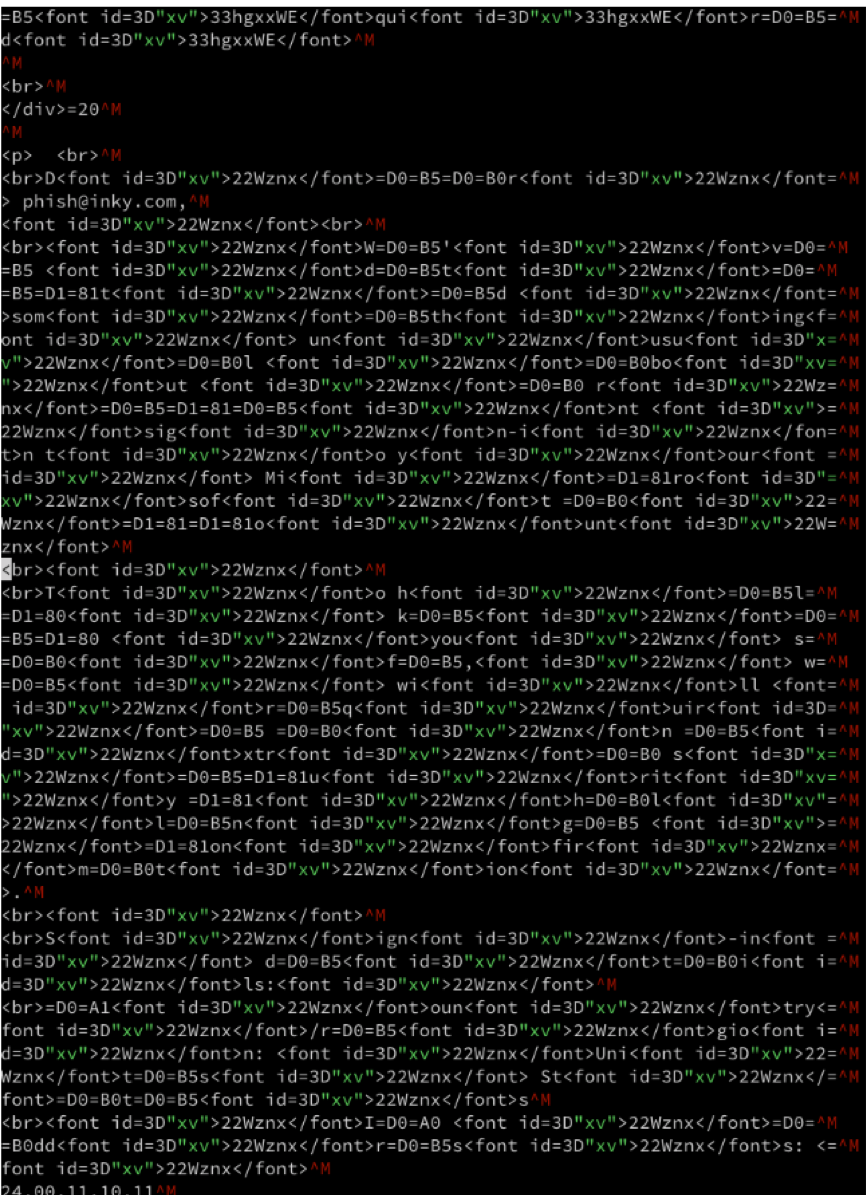
Notice all the weird font tags and gibberish showing the HTML. That gibberish was inserted by the attacker between every (visible) letter of the text, to confuse mail protection software.
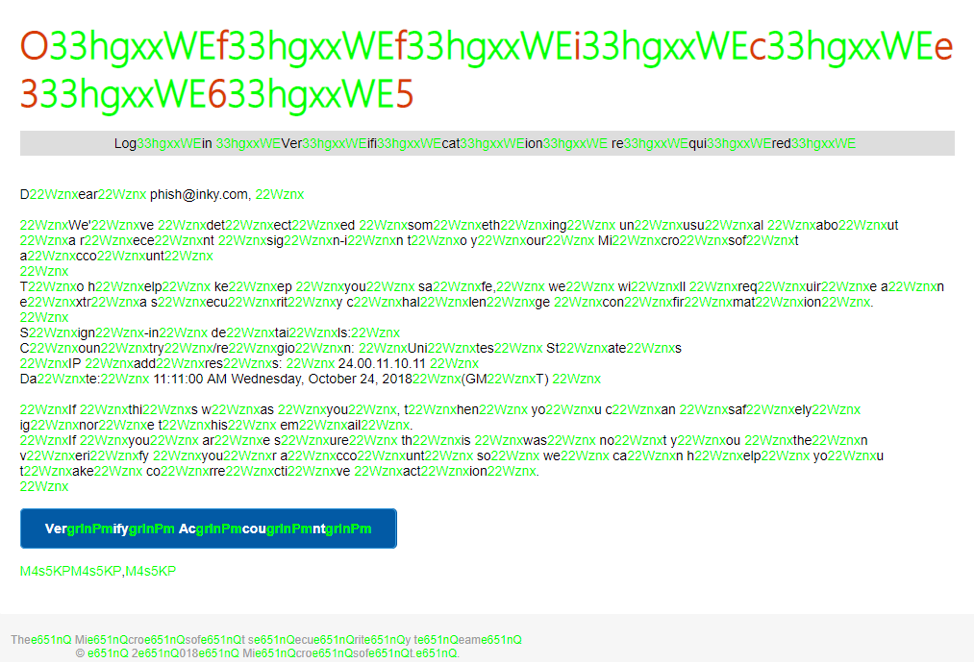
INKY's unique intelligence can "see" the email like a human would and the invisible hidden stuff. This is how INKY works:
- INKY evaluates that this email is supposed to be from Microsoft using computer vision
- INKY then looks ‘behind the scenes’ to prove the domain is actually owned by Microsoft
In this case, the email clearly is not coming from who it is purported to be from.
And this is what it looks like with the highlighted invisible code in green:
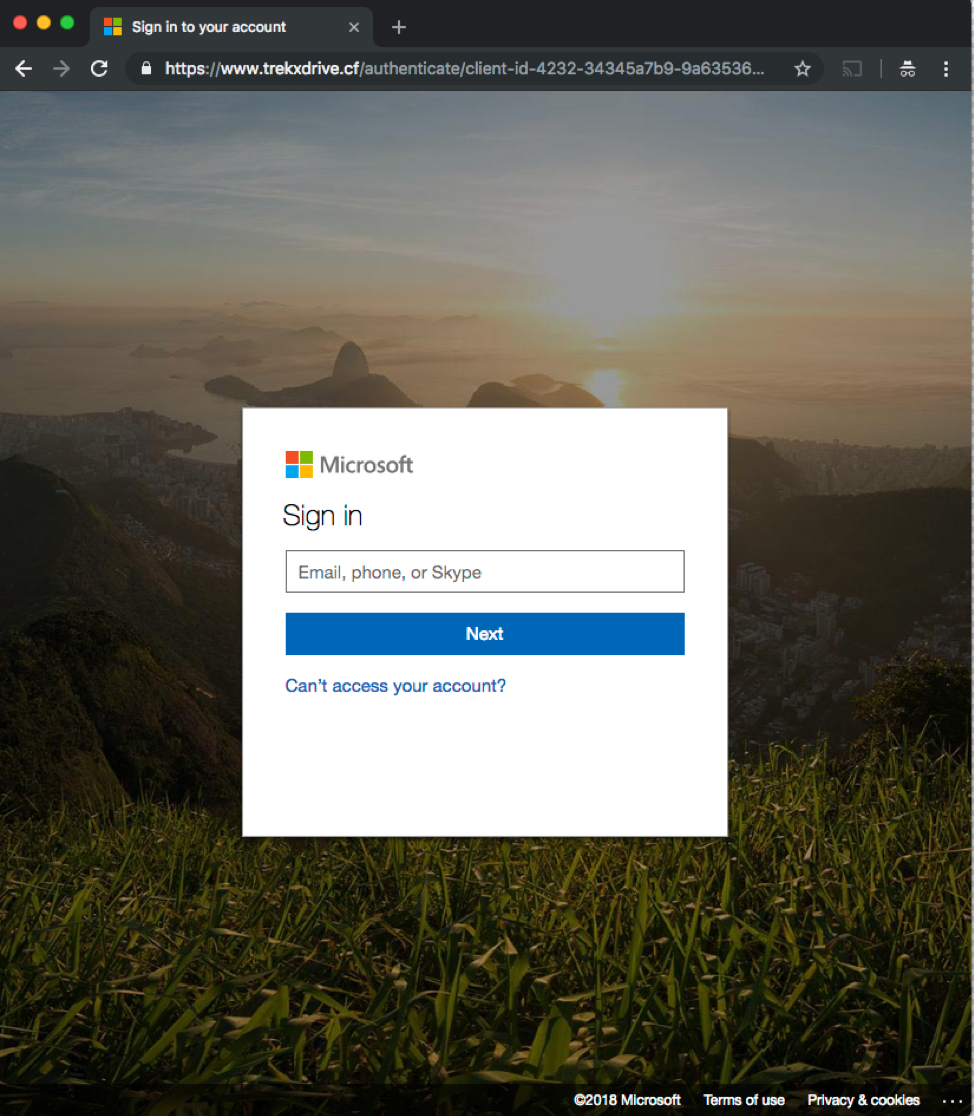
This is a very cleaver phishing attack. To the recipient if they click through the link, they are directed to an identical Office 365 login page:
INKY is the only email protection software that is equipped to deal with a challenge that has grown increasingly targeted, sophisticated, and lethal. A single focused attack like the above example can cripple an organization overnight. Signs of fraud are becoming harder and harder to detect and this is exactly why INKY exists. INKY is the new solution in the war against phishing and the smartest investment you can make in the security of your organization.
Are you looking for the best solution out there to protect your organization from these types of attacks?
Request a demo of INKY today, to let us show you how our technology is leagues above the rest.



